Small and medium-sized enterprises (SMEs) have long been the “soft underbelly” of the digital economy, often lacking the budget and specialized personnel required to maintain robust cybersecurity defenses. This vulnerability is now being addressed through a strategic partnership aimed at integrating high-level security directly into the infrastructure layer.
On April 6, 2026, cyber threat management specialist Naru Security and hosting service provider Viaweb (Korea IDC) announced the signing of a Memorandum of Understanding (MOU) to develop and launch a zero trust hosting model specifically designed for small and medium-sized enterprises via Byline Network. The collaboration seeks to eliminate “security blind spots” by providing automated threat detection and expert analysis without requiring customers to deploy separate software or hire dedicated security teams.
The initiative comes at a critical time as the diversification of attack vectors—driven by the proliferation of cloud computing and remote work—has made traditional perimeter-based security obsolete. By embedding security into the hosting environment, the two companies aim to lower the barrier to entry for professional-grade protection, aligning with current government policy trends to support SME security infrastructure via Money Today.
Integrating ZeroTiCA with Hosting Infrastructure
At the heart of this new model is the combination of Naru Security’s “ZeroTiCA,” a subscription-based breach evaluation service, and Viaweb’s established hosting infrastructure. This integration transforms the hosting environment from a passive storage and delivery system into an active security layer.
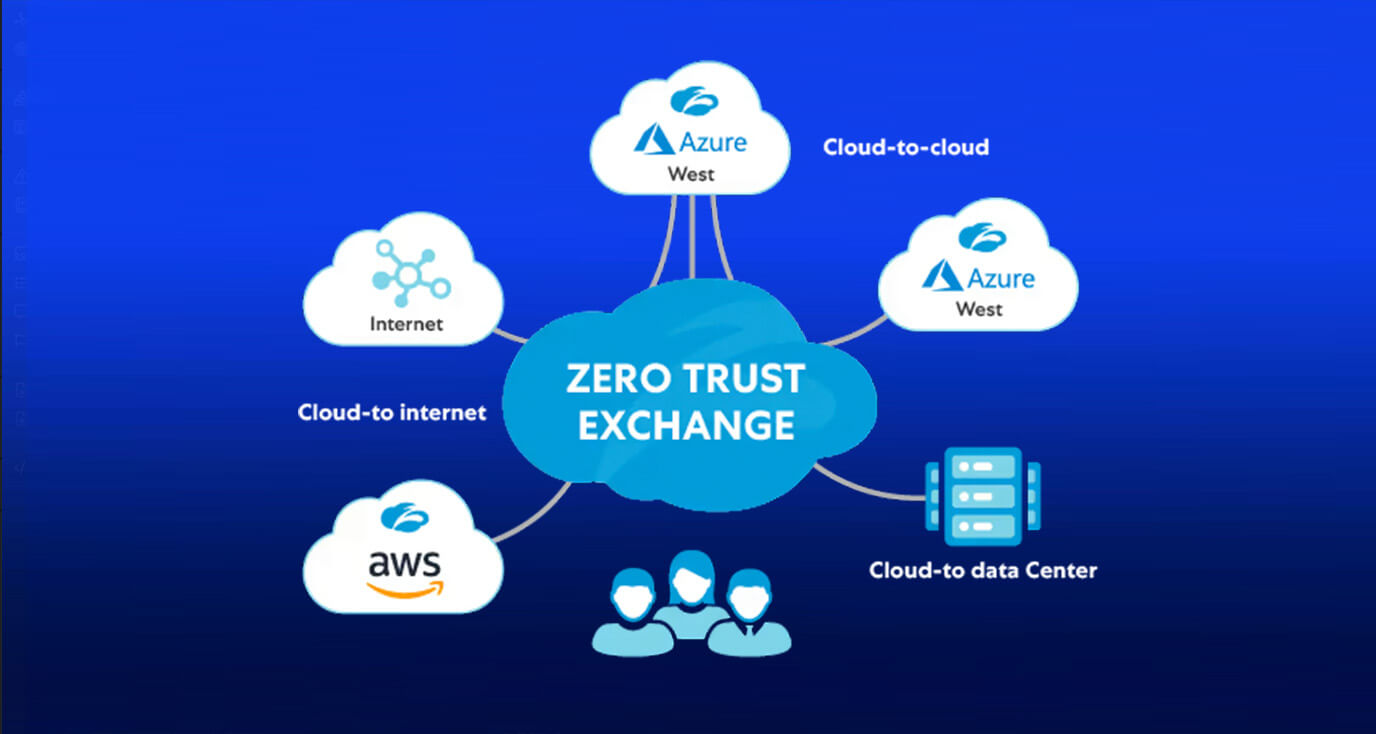
Zero trust is a security framework based on the principle of “never trust, always verify.” Rather than assuming everything inside a corporate network is safe, a zero trust architecture requires continuous verification of every user and device attempting to access resources. In the context of this hosting model, the system monitors network data generated within the hosting environment to identify anomalies in real-time.
Once an anomaly is detected, the process moves beyond automated alerts. Security experts then step in to verify whether the anomaly constitutes an actual breach. This hybrid approach—combining automated detection with human intelligence—ensures that SMEs receive the same level of scrutiny as larger corporations that can afford full-scale Security Operations Centers (SOCs) via ZDNet Korea.
Key Pillars of the Naru Security and Viaweb Partnership
The MOU outlines several core areas of cooperation intended to scale the reach of the zero trust hosting model:
- Joint Development and Operation: The companies will collaborate on the technical development of hosting-based zero trust services to ensure seamless integration between the security layer and the server infrastructure.
- Data Collection and Analysis: The partnership focuses on the systematic collection of security data and the provision of advanced threat analysis to preemptively identify risks.
- Market Expansion: Through joint sales and marketing efforts, the two firms intend to reach a broader segment of the SME and mid-market sectors that currently lack adequate protection.
Addressing the SME Security Gap
The urgency of this collaboration is underscored by the rising frequency of targeted attacks on smaller businesses. Ransomware, personal information leaks, and web-shell attacks have become increasingly common, yet many SMEs find the cost of professional security tools prohibitive. The shift toward remote work has expanded the “attack surface,” giving hackers more entry points than ever before via Money Today.

By offering a model where threat response is bundled with the server and hosting service, Naru Security and Viaweb are shifting the burden of security from the customer to the provider. This “security-as-a-service” approach means that a business owner does not need to be a cybersecurity expert to protect their data; the protection is inherent in the infrastructure they already use.
Kim Hyuk-jun, CEO of Naru Security, characterized the project as the first hosting-infrastructure-based security model in South Korea, emphasizing that it allows for threat response without the need for separate personnel or complex systems via ZDNet Korea.
Comparison of Traditional vs. Zero Trust Hosting
| Feature | Traditional SME Security | Zero Trust Hosting Model |
|---|---|---|
| Implementation | Requires separate software/hardware installation | Integrated into hosting infrastructure |
| Staffing | Requires dedicated security personnel or consultants | Managed by provider’s security experts |
| Detection Method | Often reactive (detected after a breach) | Proactive (anomaly detection via network data) |
| Cost Structure | High upfront CAPEX for solutions | Subscription-based via ZeroTiCA and hosting |
What This Means for the Industry
The move toward zero trust hosting reflects a broader global trend in cybersecurity where the “perimeter” is no longer a physical office wall but a dynamic identity and data verification process. For the tech industry, this signals a shift toward “invisible security,” where protection is embedded so deeply into the utility of the cloud that the end-user experiences it as a standard feature rather than an add-on.
As government policies continue to push for higher security standards for smaller enterprises, the partnership between Naru Security and Viaweb provides a scalable blueprint for how infrastructure providers can act as the first line of defense for the digital economy.
The next phase of this collaboration will involve the operational rollout of the joint services and the expansion of the joint marketing campaign to target mid-sized enterprises. Further updates on the specific service tiers and pricing for the zero trust hosting model are expected as the joint development phase progresses.
If you are an SME owner or a tech professional interested in the evolution of zero trust architectures, we invite you to share your thoughts in the comments below or share this analysis with your network.