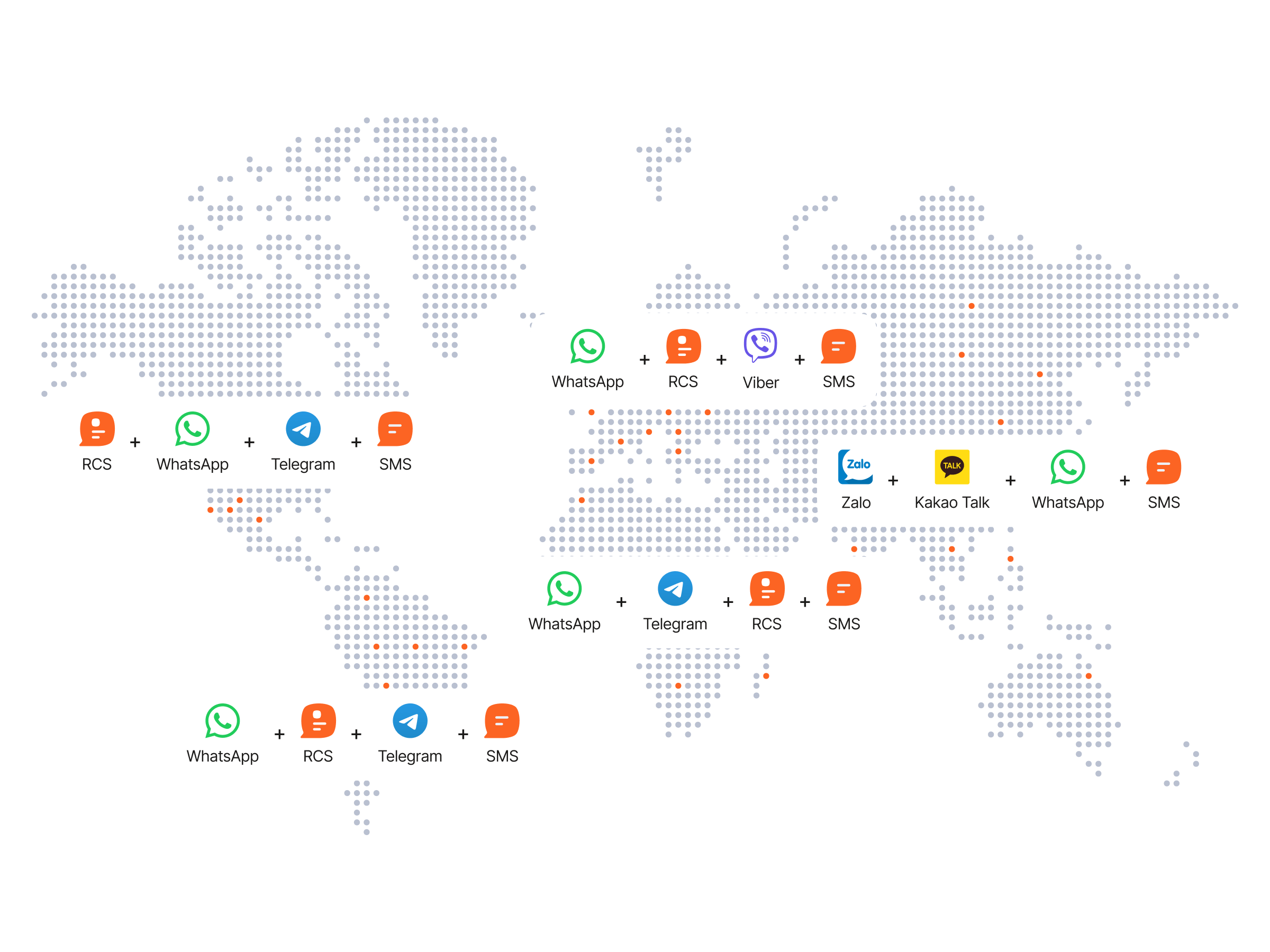
For millions of smartphone users, the notification chime of a new message is usually a welcome sound. However, in recent years, that chime has increasingly signaled the arrival of unsolicited advertisements, fraudulent schemes, and bulk-sent spam. While traditional SMS spam was once the primary nuisance, a sophisticated underground economy has emerged, leveraging advanced protocols like Rich Communication Services (RCS) and encrypted platforms such as WhatsApp and Telegram to bypass security filters.
This “grey market” of messaging operates through a complex network of “source server rooms” (often referred to as 机房 in Chinese marketing circles) and account wholesalers who sell bulk-access capabilities to the highest bidder. These operations do not merely send messages. they provide the infrastructure—virtual numbers, automated scripts, and “hardened” accounts—necessary to conduct mass outreach while evading the aggressive anti-spam algorithms employed by tech giants.
As a technology journalist who has tracked the evolution of software engineering and digital communication, I have observed a troubling trend: the professionalization of spam. What was once the domain of amateur “scripters” has evolved into a global supply chain. From the promotion of “one-way” and “two-way” RCS messaging to the sale of verified Telegram accounts, these services represent a significant challenge to the integrity of our digital communication channels.
The Mechanics of Modern Bulk Messaging
To understand how these operations function, one must first understand the tools they exploit. The modern spam ecosystem relies heavily on the distinction between different messaging protocols and the ability to generate massive quantities of unique identities.
RCS: The New Frontier for Spam
Rich Communication Services (RCS) was designed to replace the aging SMS standard, bringing features like read receipts, high-resolution media sharing, and typing indicators to the native messaging app. While it enhances user experience, it also provides a more lucrative playground for bulk senders. In the underground market, providers often distinguish between “one-way” (单向) and “two-way” (双向) RCS messaging.
One-way messaging is primarily used for broadcasting—sending a blast of messages to thousands of recipients without the capacity or intent to receive a reply. Two-way messaging is more sophisticated, allowing the sender to engage in dialogue, which is often used in more targeted social engineering or phishing attacks. Because RCS is integrated directly into the operating system of Android devices and is increasingly supported by Apple through GSMA standards, the reach of these messages is nearly universal across the smartphone market.
The “Source Server Room” (机房) Ecosystem
The term “source server room” refers to the physical and virtual infrastructure used to host thousands of virtual SIMs or API-driven accounts. Rather than using a single phone, these operations use “SIM farms”—hardware racks that can hold hundreds of SIM cards simultaneously—or exploit vulnerabilities in VoIP (Voice over IP) providers to generate phone numbers in bulk.
These “source” providers are the wholesalers of the spam world. They sell access to these numbers and the software to automate them to “resellers,” who then market the services on platforms like X (formerly Twitter) and Telegram. These ads often promise “global supply” and “six-digit number” verification, referring to the specific patterns of phone numbers or the ability to bypass the two-factor authentication (2FA) codes required to register new accounts.
Exploiting Encrypted Platforms: WhatsApp and Telegram
While RCS targets the native dialer, a huge portion of the grey market focuses on “Over-the-Top” (OTT) apps like WhatsApp and Telegram. These platforms are prized by spammers because they offer a higher perceived trust level than a random SMS.

WhatsApp, in particular, has stringent policies against bulk messaging. To circumvent this, account wholesalers sell “aged” accounts—profiles that were created months or years ago—which are less likely to be flagged as bots by Meta’s security systems. The “two-way bulk sending” (双向群发) mentioned in underground advertisements refers to tools that can automate the sending of messages while also simulating human behavior, such as waiting for a reply or interacting with the user, to avoid detection.
Telegram is similarly targeted due to its open API and the ease with which groups and channels can be created. “Source” providers offer specialized “bot farms” that can flood groups with messages or create thousands of fake members to give a channel a veneer of legitimacy. This infrastructure is frequently used not only for commercial spam but also for coordinated disinformation campaigns.
The Risks to the End User
The proliferation of these bulk messaging services is not merely a nuisance; We see a security risk. When a user receives a message from a “verified” looking account or a rich-media RCS message, the likelihood of a successful phishing attack increases.
- Social Engineering: By using “two-way” messaging, attackers can build rapport with a victim over several messages before sending a malicious link.
- Data Harvesting: Many of these bulk services are used to verify if a phone number is “active.” Once a user responds, their number is marked as “live” and sold to other, more malicious actors.
- Credential Theft: The “six-digit numbers” and account-selling services often rely on hijacking existing accounts via SIM swapping or exploiting vulnerabilities in SMS-based 2FA.
For those looking to protect themselves, the most effective defense is a combination of platform-level filters and personal vigilance. Most modern smartphones allow users to “Report and Block” unknown senders, which feeds data back into the platform’s AI to help identify and shut down the “server rooms” providing the infrastructure.
The Regulatory and Technical Battle
The fight against bulk messaging is an arms race. As platforms improve their detection, spammers find new ways to mimic human behavior. Meta and Google have invested heavily in machine learning models that analyze metadata—such as the speed of message delivery, the similarity of message content, and the reputation of the originating IP address—to stop spam in real-time.
However, the global nature of this business makes enforcement difficult. A “server room” might be located in one jurisdiction, the account wholesaler in another, and the end customer in a third. This fragmentation allows these operations to persist despite the efforts of regulatory bodies like the Federal Trade Commission (FTC) in the U.S. Or the GDPR enforcement agencies in Europe, which penalize unauthorized commercial communications.
The industry is now moving toward “Verified Business” profiles, where companies must undergo a rigorous verification process to send bulk notifications. While this helps legitimate businesses, it further pushes the “grey market” into the shadows, where they use stolen or synthetic identities to appear legitimate.
Comparison of Messaging Spam Methods
| Channel | Primary Method | Spammer’s Goal | Detection Difficulty |
|---|---|---|---|
| RCS | API/SIM Farm Integration | Mass Brand Awareness/Phishing | Medium (OS Level) |
| Aged Account Reselling | High-Trust Social Engineering | High (End-to-End Encrypted) | |
| Telegram | Bot API/Group Flooding | Disinformation/Mass Marketing | Low to Medium |
| SMS | SMS Gateways/SMPP | Quick-Hit Scams/Links | Low (Highly Filtered) |
Looking Ahead: The Future of Communication Security
As we move deeper into the era of AI, the threat of bulk messaging will only grow. We are already seeing the rise of AI-generated scripts that can personalize thousands of messages in real-time, making them nearly indistinguishable from human conversation. The “two-way” messaging services of today will likely evolve into AI-driven chatbots that can conduct full-scale fraud operations without a human operator ever touching a keyboard.
The solution will likely require a shift away from phone-number-based identity. As long as the phone number is the primary key for account creation and verification, the “account wholesaler” industry will thrive. Moving toward decentralized identity (DID) or hardware-based authentication (like FIDO2) could eventually render the “source server room” obsolete.
Until then, the burden of security remains shared between the platforms that provide the service and the users who consume it. The presence of advertisements for “global supply” of accounts on social media is a stark reminder that our communication infrastructure is being weaponized by a professionalized class of digital opportunists.
The next major checkpoint in this battle will be the continued rollout of RCS across all major mobile ecosystems and the subsequent updates to spam filtering protocols. As Apple and Google further synchronize their messaging standards, People can expect a new wave of “cross-platform” spam tools to emerge, followed by an equally aggressive response from security researchers.
Do you frequently receive unsolicited RCS or encrypted messages? How has your experience with platform filters been? Share your thoughts and experiences in the comments below.