When we trust an AI tool to restore a precious memory—a corrupted wedding photo or a grainy family video—we assume the technology is working solely for our benefit. However, a recent discovery regarding a Wondershare RepairIt security breach suggests that for some users, that trust may have been misplaced, exposing sensitive personal data to potential exploitation.
Researchers from Trend Micro have revealed that Wondershare RepairIt, an AI-driven application designed to enhance and repair images and videos, suffered from critical security lapses. The findings indicate that the application not only leaked private user data but also exposed proprietary company assets, creating a significant window of opportunity for sophisticated cyberattacks.
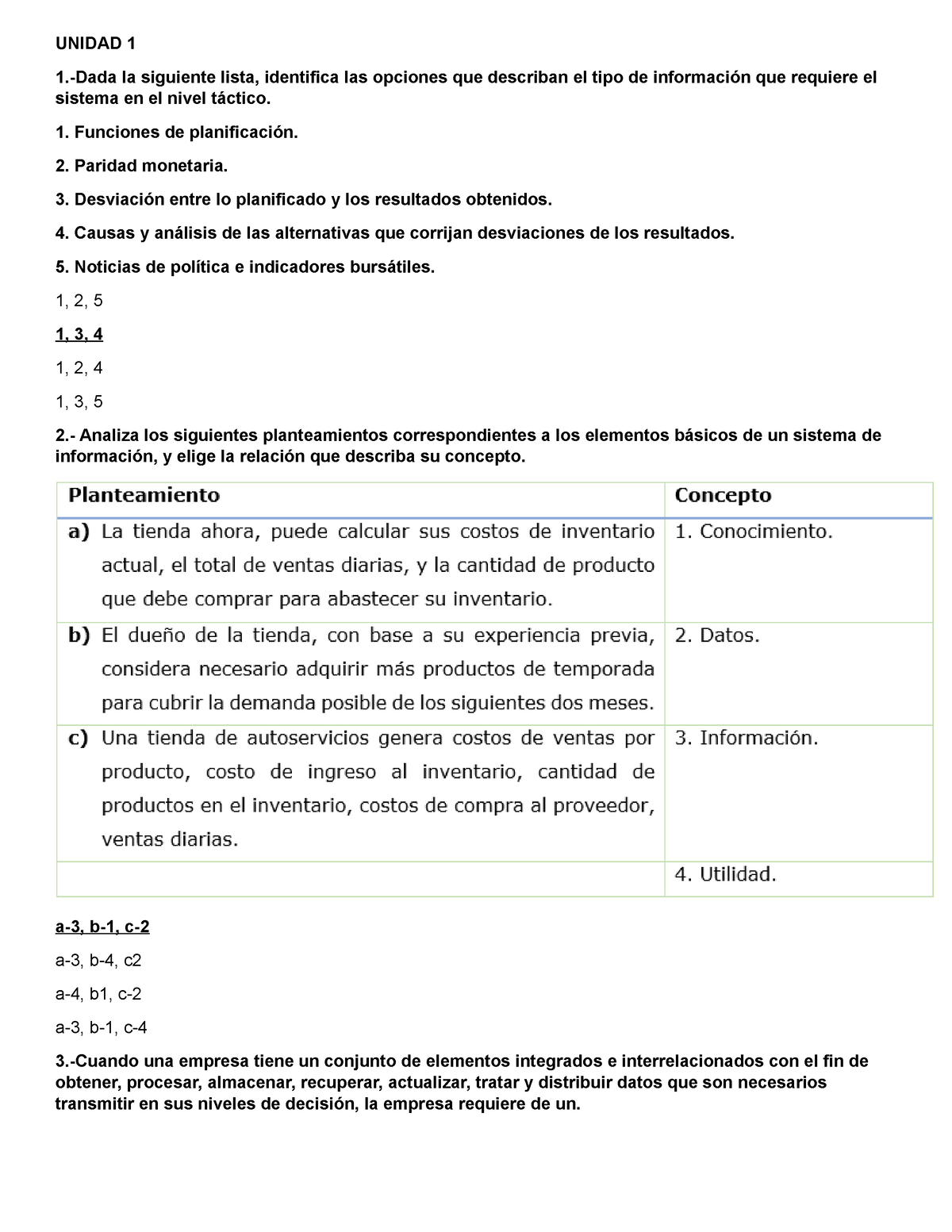
The breach is the result of what researchers describe as poor Development, Security, and Operations (DevSecOps) practices. By embedding highly permissive cloud access tokens directly into the application’s code, the developers inadvertently provided a “master key” to anyone with the technical knowledge to find it.
This vulnerability is particularly concerning because it contradicts the company’s own public assurances. While the application and its website explicitly stated that user data would not be stored, the investigation found that the company was indeed collecting and retaining sensitive user photos and videos.
Hardcoded Credentials: The Open Door to User Data
The core of the issue lies in the use of hardcoded credentials. In software development, “hardcoding” occurs when a programmer embeds sensitive information—such as passwords, API keys, or access tokens—directly into the source code rather than using a secure vault or environment variable. When this code is compiled into a binary and distributed to users, those secrets can be extracted through a process called static analysis.
During their investigation, Trend Micro researchers analyzed the Wondershare RepairIt binary and discovered hardcoded access credentials for a cloud storage service. These credentials granted both read and write permissions to a cloud bucket, effectively bypassing the security measures that should have protected the data stored within.
The consequences of this oversight were extensive. The exposed cloud storage contained thousands of user-uploaded images and videos, with some files dating back more than two years. Because the data was unencrypted and the access tokens were overly permissive, these private files were vulnerable to unauthorized access.
Beyond User Privacy: The Risk of Supply Chain Attacks
While the leak of personal photos is a grave privacy violation, the security implications extend far beyond individual users. The compromised cloud bucket did not just hold user data; it also contained critical company infrastructure, including:

- AI model files and their associated configurations.
- Signed binaries and application executables.
- Container images and internal company source code.
The presence of signed binaries and AI models in an insecure environment introduces the risk of a supply chain attack. In a typical supply chain attack, a threat actor compromises a trusted vendor’s software build process to distribute malware to the vendor’s entire customer base. Because the binaries in the cloud bucket were “signed”—meaning they carry a digital signature proving they come from the legitimate vendor—attackers could potentially replace a legitimate file with a malicious one.
If an attacker were to manipulate an AI model or an executable file and upload it back to the bucket, the application might distribute these malicious payloads to users through official software updates or AI model downloads. Users would have no reason to suspect the update was compromised, as it would appear to be a legitimate, vendor-signed file.
A Conflict of Privacy and Practice
For many consumers, the most jarring aspect of this discovery is the discrepancy between the company’s stated privacy policy and its actual operations. The application’s interface and website explicitly claimed that user data would not be stored. However, the discovery of thousands of images and videos in the cloud bucket confirms that this was not the case.
This gap between policy and practice is a recurring theme in the rapid deployment of AI tools. As companies rush to integrate generative AI and machine learning into consumer products, security and privacy frameworks often struggle to keep pace. In this instance, the failure to align data handling practices with privacy promises has left users exposed.
The vulnerabilities associated with this breach have been assigned official identifiers: CVE-2025-10643 and CVE-2025-10644. These designations allow security professionals and organizations to track the flaws and ensure that patches are applied across the ecosystem.
The Broader Lesson for AI Development
The Wondershare RepairIt case serves as a cautionary tale for the broader tech industry. As AI-powered applications become ubiquitous, the “attack surface” for software expands. AI models are not just mathematical formulas; they are files that can be tampered with, and the data used to train or refine them is often highly sensitive.
To prevent such breaches, organizations must adopt rigorous DevSecOps practices. This includes:
- Secret Management: Using dedicated tools like HashiCorp Vault or AWS Secrets Manager instead of hardcoding credentials.
- Least Privilege Access: Ensuring that access tokens have the absolute minimum permissions necessary to function (e.g., read-only access instead of read-write).
- Encryption at Rest: Ensuring that all user data stored in the cloud is encrypted, so that even if a bucket is exposed, the data remains unreadable.
- Regular Security Audits: Conducting third-party penetration testing and static analysis of binaries before they are released to the public.
For users, this incident highlights the importance of scrutinizing the permissions requested by AI tools and being cautious about uploading sensitive personal media to cloud-based repair services, regardless of the privacy claims made on the landing page.
Timeline of Disclosure
The path to public awareness of these vulnerabilities began months before the full report was released. Initial disclosure was made in April 2025 through the Trend Zero Day Initiative (ZDI). This process is designed to give vendors a window of time to fix vulnerabilities before they are made public to prevent attackers from exploiting the flaw in the interim.

Despite this early warning, the detailed analysis published by Trend Micro Research on September 23, 2025, noted that Wondershare had not responded to the report as of the time of publication. This lack of communication further complicates the situation for users who may still be using vulnerable versions of the software.
As the industry continues to move toward an AI-first approach to creativity and utility, the integrity of the software supply chain and the honesty of privacy policies will remain the primary benchmarks of a company’s reliability.
We will continue to monitor for an official response or a security patch from Wondershare regarding CVE-2025-10643 and CVE-2025-10644. Users are encouraged to keep their software updated and review their privacy settings.
Do you use AI-powered tools for your personal media? How much do you trust the privacy policies of these applications? Share your thoughts in the comments below.